Introduction
In an era where data breaches and system failures can severely impact businesses in an instant, the significance of effective backup vendor management is paramount. Organizations can reap substantial benefits by adopting best practices for outsourcing these vital services, ranging from improved data security to expedited recovery times. Yet, a pressing question persists: how can companies select the right partners and maintain effective oversight in a swiftly changing technological environment? This article explores four essential practices that can elevate the outsourced management of backup vendors into a strategic asset, ensuring business continuity and resilience.
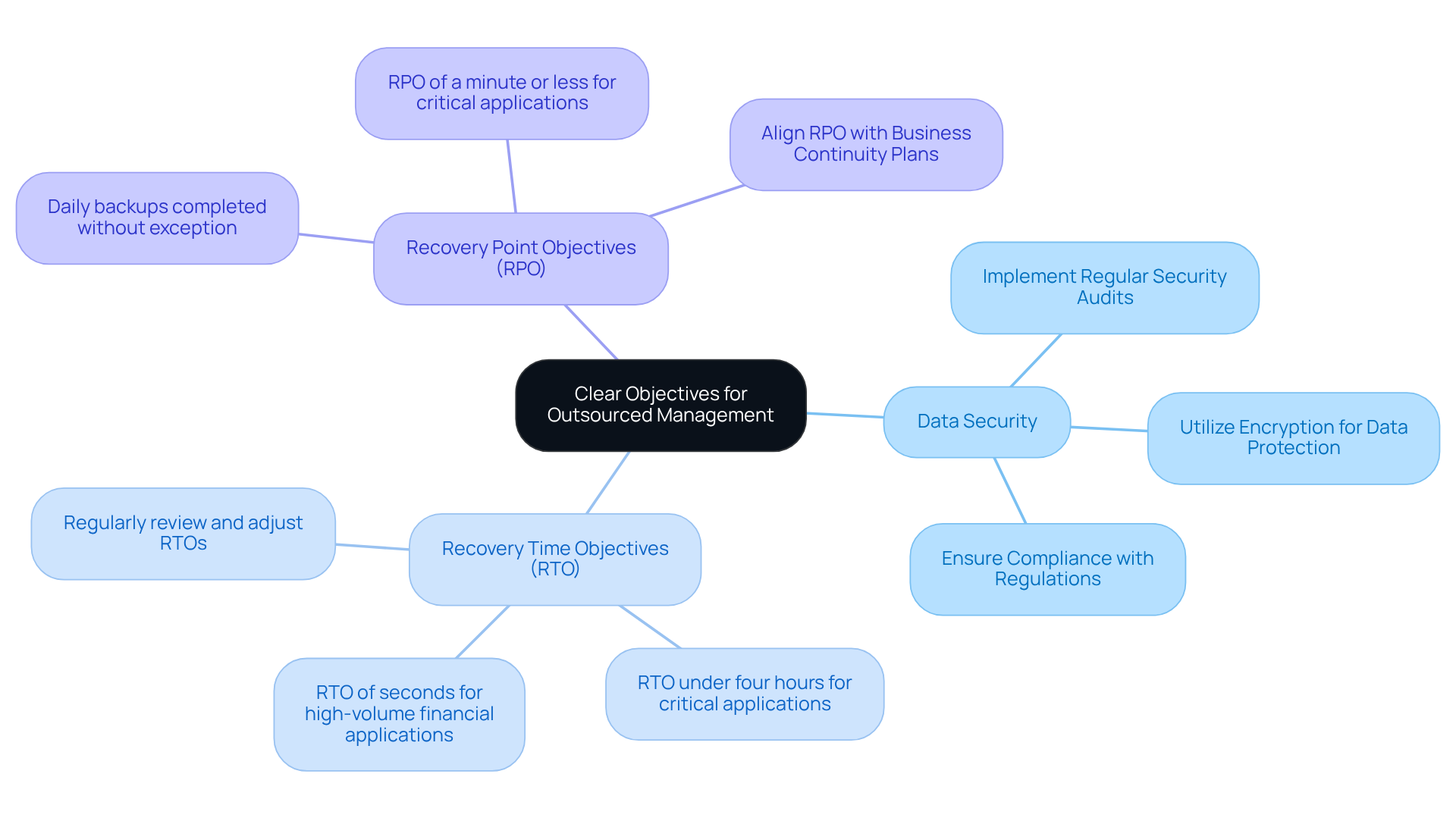
Establish Clear Objectives for Outsourced Management
To effectively implement outsourcing, companies must establish clear objectives and metrics that define success in key areas such as data security, recovery time objective (RTO), and compliance. For instance, a business might aim for an RTO of under four hours for critical applications or ensure that daily backups are completed without exception. By articulating these objectives, companies can clearly communicate their expectations to suppliers, fostering alignment from the outset with their service providers.
Regularly revisiting these objectives is crucial to adapt to changing business needs and technological advancements. In 2026, the average RTO for businesses is expected to vary significantly; critical systems may require RTOs of just a few seconds, while less critical applications could have RTOs extending to several hours. By setting clear benchmarks, organizations can enhance their operational resilience and ensure that their backup strategy aligns with their operational requirements.
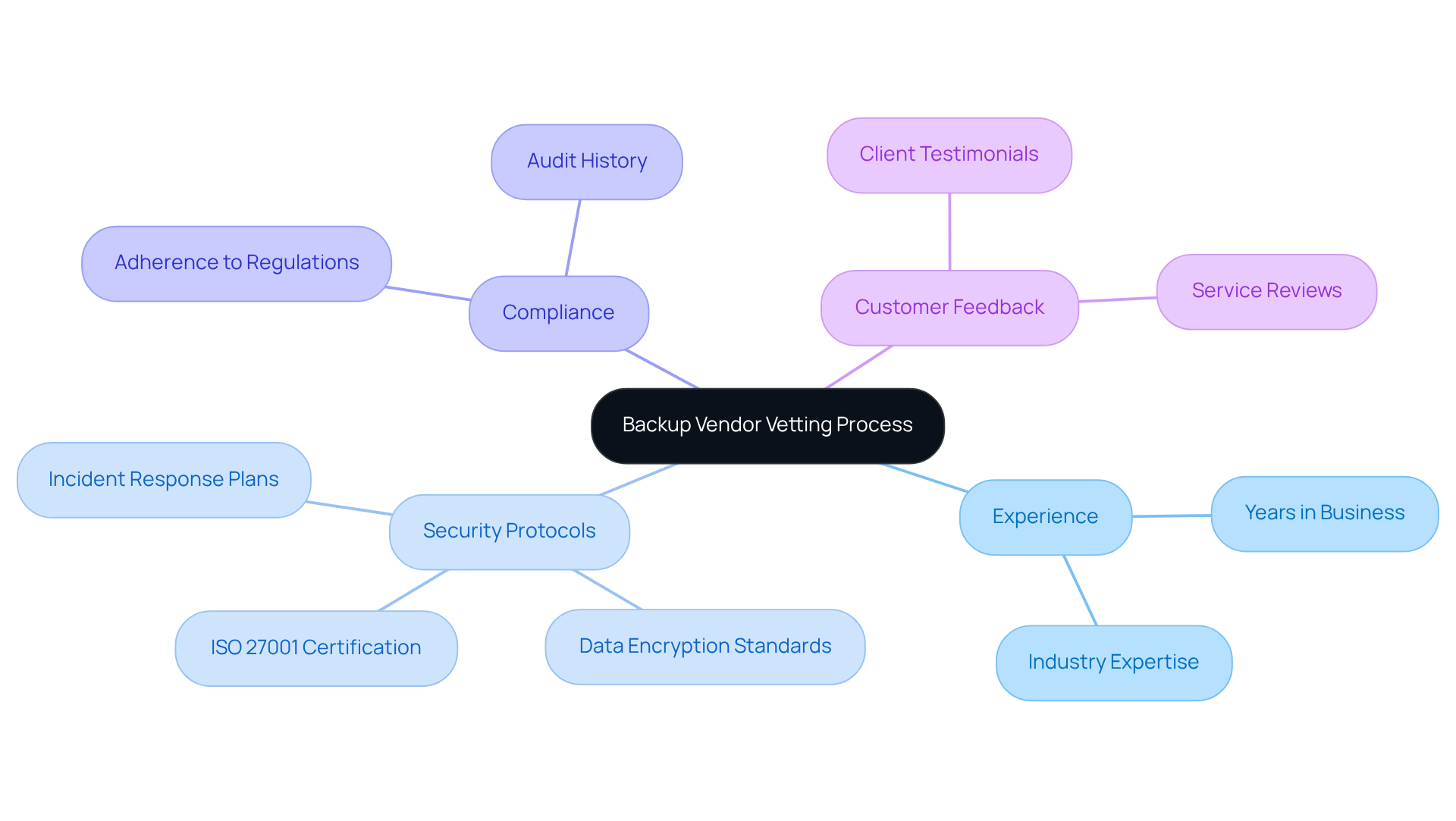
Select the Right Backup Vendors Through Rigorous Vetting
Choosing the right backup vendor involves a meticulous vetting process that rigorously evaluates potential partners against established criteria. Organizations should prioritize suppliers based on key factors such as:
- Experience
- Compliance with industry standards
For instance, requiring certifications from suppliers demonstrates a strong commitment to information security management, which is increasingly vital in today’s data-driven landscape. Additionally, conducting thorough background checks and requesting references can yield valuable insights into a supplier's reliability and historical performance.
This careful vetting process not only helps identify the most suitable supplier but also lays the groundwork for a successful partnership. Ultimately, this enhances security and strengthens trust.
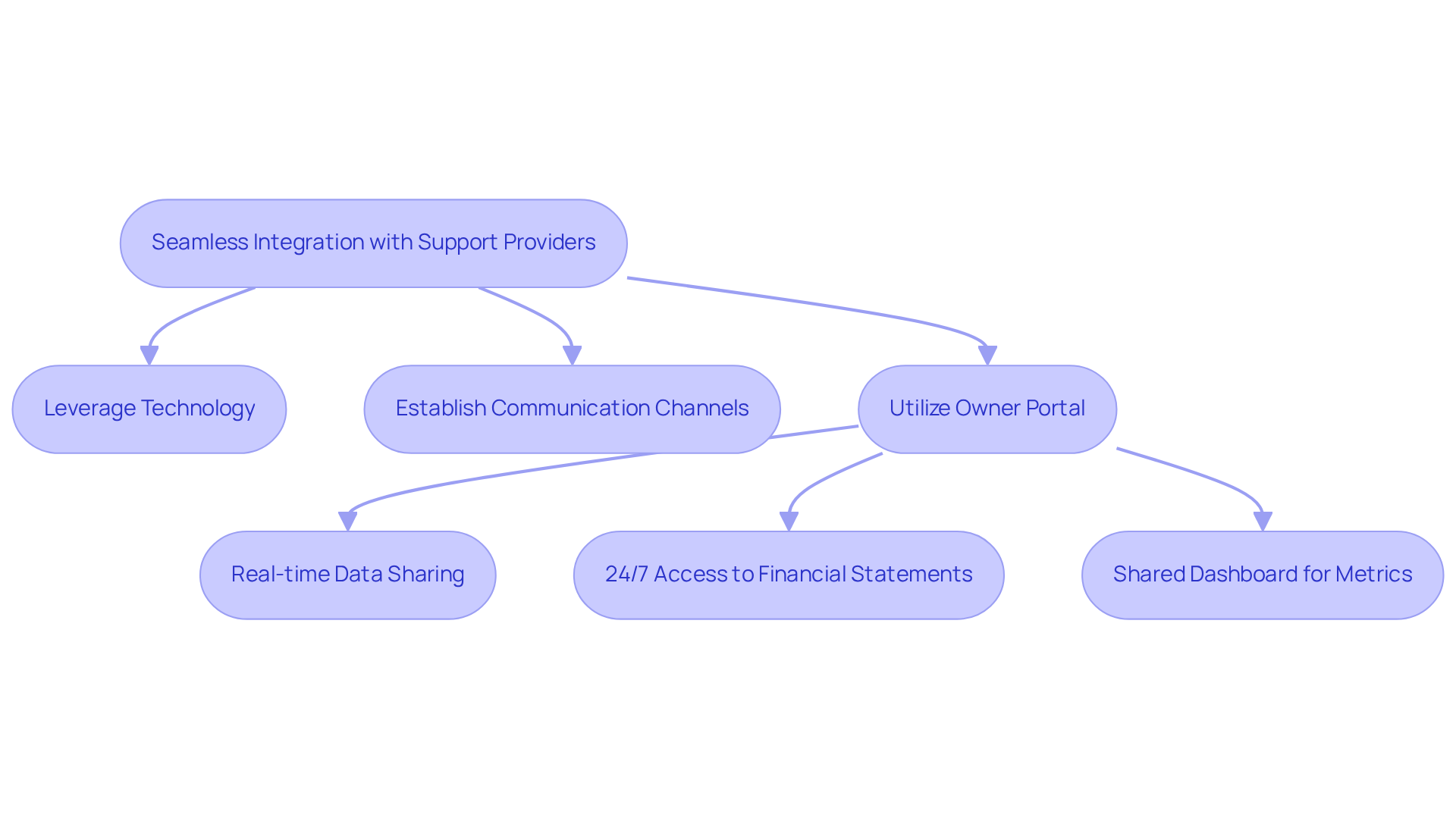
Leverage Technology and Communication for Seamless Integration
To ensure seamless integration with support providers, companies must leverage technology and establish clear communication. Utilizing The Housing Guild's platform, which offers strong mobile features, facilitates real-time data sharing and monitoring, keeping both parties informed about status updates and potential issues. With reports, monthly summaries, and essential documents, property owners can remain connected and well-informed.
Regular check-ins through video conferencing or project management tools can promote open communication, allowing for prompt resolution of any concerns. For instance, developing a communication plan can support the outsourced management for backup vendors, ensuring both the company and the supplier stay aligned on goals and performance expectations.
As Tim Roddy highlights, "World Backup Day serves as a crucial reminder that backup management isn’t just about having a copy of your data; it’s about ensuring business continuity with minimal disruption." This underscores the importance of utilizing the features of technology to maintain productive relationships.
Data indicates that best practices, such as those found in industry reports, significantly enhance supplier management, with 94% of organizations reporting improved collaboration and accountability when implementing effective strategies. By prioritizing these practices, businesses can mitigate risks and enhance the overall effectiveness of their vendor management.
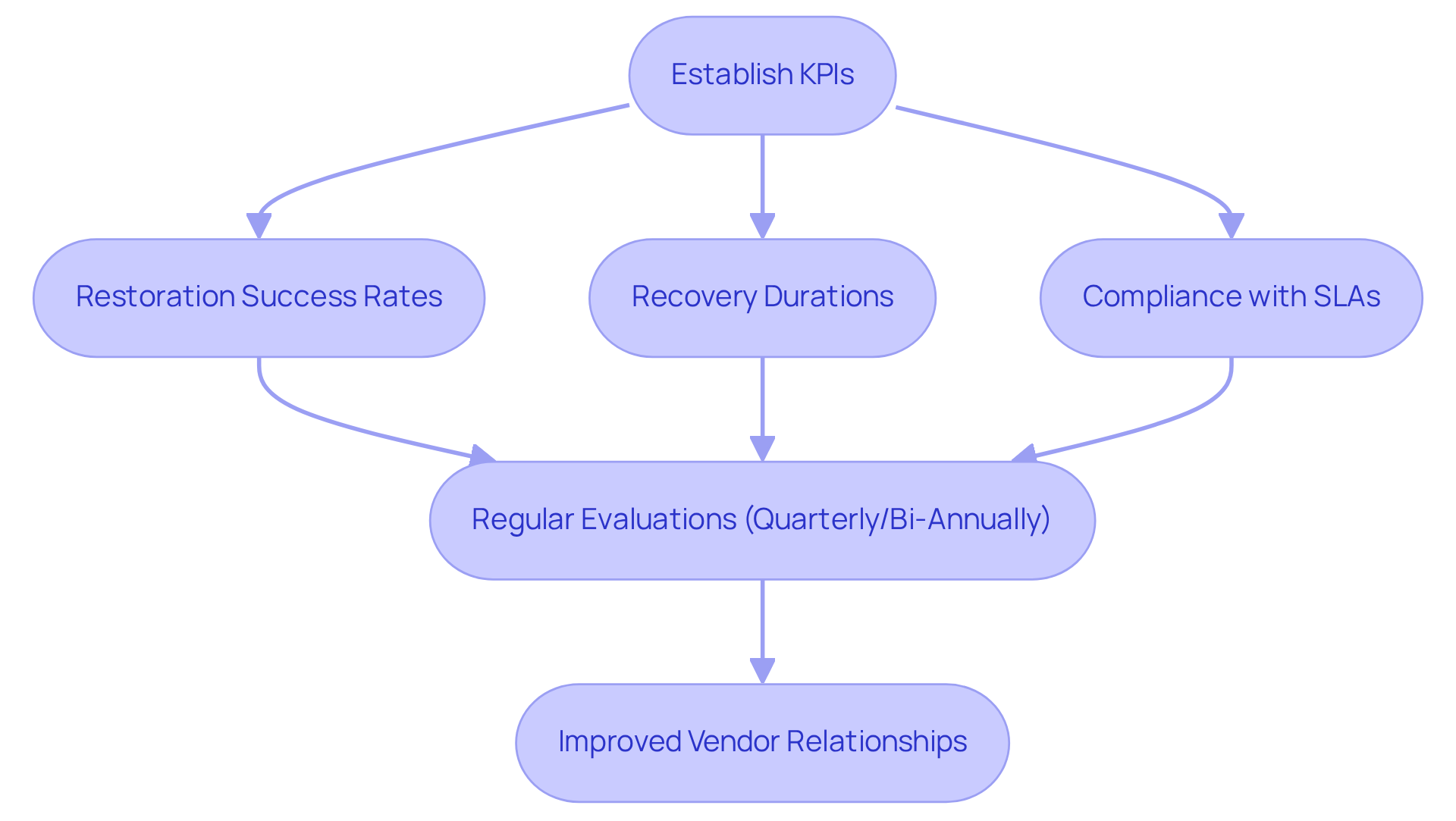
Monitor and Evaluate Vendor Performance Regularly
To maintain robust vendor relationships, companies should implement a systematic approach for performance evaluation. This process begins with the establishment of metrics that align with the objectives defined at the outset of the partnership. For example, organizations might track metrics such as restoration success rates, which typically average around 95% across various sectors, indicating a reliable backup solution. Other important metrics include recovery durations and compliance with service level agreements.
Regular assessments provide valuable insights into vendor performance and highlight areas for improvement. By cultivating an environment of accountability and transparency, organizations can ensure that their backup vendors consistently meet their evolving needs.
Conclusion
Establishing effective outsourced management for backup vendors is essential for organizations seeking to bolster their data security and operational resilience. By defining clear objectives and measurable goals, businesses can align their expectations with those of their suppliers, paving the way for successful partnerships. The need for continuous adaptation to evolving technological landscapes and business needs further highlights the importance of these foundational practices.
This article outlines four essential best practices:
- Setting clear objectives
- Rigorously vetting potential backup vendors
- Leveraging technology for seamless integration
- Regularly monitoring vendor performance
Each of these elements plays a crucial role in creating a robust framework for managing backup vendors, ensuring that organizations can effectively respond to data management challenges while upholding high standards of security and compliance.
Ultimately, the significance of these practices cannot be overstated. As organizations increasingly depend on outsourced backup solutions, implementing these strategies will not only safeguard data but also cultivate long-term, productive relationships with vendors. By prioritizing effective management of backup vendors, businesses can enhance their overall resilience and ensure continuity in their operations, setting the stage for success in an ever-evolving digital landscape.
Frequently Asked Questions
What is the importance of establishing clear objectives for outsourced management of backup vendors?
Establishing clear objectives is crucial as it defines success in key areas such as data security, recovery time objectives (RTO), and recovery point objectives (RPO), allowing companies to communicate their expectations effectively to suppliers.
What are some examples of measurable goals for outsourced backup management?
Examples of measurable goals include aiming for an RTO of under four hours for critical applications and ensuring that daily backups are completed without exception.
Why is it important to regularly revisit the established objectives?
Regularly revisiting objectives is important to adapt to changing business needs and technological advancements, ensuring that the goals remain relevant and effective.
How are RTO expectations expected to change by 2026?
By 2026, the average RTO for businesses is expected to vary significantly, with critical systems potentially requiring RTOs of just a few seconds, while less critical applications may have RTOs extending to several hours.
How can setting measurable goals enhance data protection strategies?
Setting measurable goals allows organizations to better align their outsourced management for backup vendors with their operational requirements, ultimately enhancing their data protection strategies.
List of Sources
- Establish Clear Objectives for Outsourced Management
- How to Build a Critical Incident Response Team for Disaster Recovery (https://backblaze.com/blog/disaster-recovery-101-improving-rto-and-rpo-goals-with-the-cloud)
- RTO vs RPO: What They Mean and How To Set Targets (https://veeam.com/blog/recovery-time-recovery-point-objectives.html)
- infrascale.com (https://infrascale.com/recovery-time-objective-rto-explained)
- 25 Business Continuity Statistics You Need to Know (https://invenioit.com/continuity/business-continuity-statistics?srsltid=AfmBOopvWOlcKJQl1aq-QH6MW41IUEIO74ruSehIBYxEauD7Q2CN4hxp)
- Select the Right Backup Vendors Through Rigorous Vetting
- 110 security and compliance statistics for tech leaders to know in 2025 (https://vanta.com/resources/compliance-statistics)
- 130+ Compliance Statistics & Trends to Know for 2026 (https://secureframe.com/blog/compliance-statistics)
- ISO 27001 isn’t just for big corporations. Here is why. (https://friggp2c.com/why-iso-27001-certification-for-small-businesses-works-in-2025)
- srm-solutions.com (https://srm-solutions.com/blog/the-number-of-iso-27001-certified-businesses-is-growing-and-heres-why)
- 62 World Backup Day Quotes from 51 Experts for 2024 (https://solutionsreview.com/backup-disaster-recovery/world-backup-day-quotes-from-experts-for-2024)
- Leverage Technology and Communication for Seamless Integration
- 49 Cloud Computing Statistics for 2025 (Trends & Insights) (https://n2ws.com/blog/cloud-computing-statistics)
- World Backup Day Quotes from Experts for 2025 - Best Backup and Disaster Recovery Tools, Software, Solutions & Vendors (https://solutionsreview.com/backup-disaster-recovery/world-backup-day-quotes-from-experts-for-2025)
- The Latest Cloud Computing Statistics (updated October 2025) | AAG IT Support (https://aag-it.com/the-latest-cloud-computing-statistics)
- infrascale.com (https://infrascale.com/data-backup-solutions-statistics-usa)
- Key Components of a Successful Vendor Communication Plan (https://panorays.com/blog/vendor-communication-plan)
- Monitor and Evaluate Vendor Performance Regularly
- Top 15 Supplier Performance Management KPIs (https://kodiakhub.com/blog/supplier-performance-management-kpis)
- Vendor Management KPIs You Need to Track in 2025 - SupplierGateway (https://suppliergateway.com/vendor-management-kpis-you-need-to-track-in-2025)
- Essential KPIs to Track Backup Performance (https://novabackup.com/blog/measuring-backup-performance-essential-kpis)
- A Complete Guide to Monitoring, Optimizing, and Tracking Vendor Performance (https://servicechannel.com/reports/supplier-performance)
- Vendor Risk Monitoring: Best Practices for Effective Management (https://supplywisdom.com/resources/vendor-risk-monitoring-best-practices-for-effective-management)

